Introduction
Azure manages and controls identity and user access to enterprise environments, data, and applications by federating user identities to Azure Active Directory and enabling multifactor authentication for more secure sign-in. Microsoft uses stringent identity management and access controls to limit data and systems access to those with a genuine business need (least-privileged). These include Azure Active Directory reporting, Azure Key Vault logs, Azure Storage Analytics, and more. Logs from your Azure resources can be integrated with your on-premises security information and event management (SIEM) system. Identity management is the process of authenticating and authorizing security principals. It also involves controlling information about those principals (identities). Security principals (identities) may include services, applications, users, groups, etc. Microsoft identity and access management solutions help IT protect access to applications and resources across the corporate datacenter and into the cloud. Such protection enables additional levels of validation, such as Multi-Factor Authentication and Conditional Access policies. Monitoring suspicious activity through advanced security reporting, auditing, and alerting helps mitigate potential security issues. Azure Active Directory Premium provides single sign-on (SSO) to thousands of cloud software as a service (SaaS) apps and access to web apps that you run on-premises. By taking advantage of the security benefits of Azure Active Directory (Azure AD), you can,
- Create and manage a single identity for each user across your hybrid enterprise, keeping users, groups, and devices in sync.
- Provide SSO access to your applications, including thousands of pre-integrated SaaS apps.
- Enable application access security by enforcing rules-based Multi-Factor Authentication for both on-premises and cloud applications.
- Provision secure remote access to on-premises web applications through Azure AD Application Proxy.
Azure Active Directory integration with SAP Cloud Platform
Let’s integrate SAP Cloud Platform with Azure Active Directory (Azure AD). Integrating SAP Cloud Platform with Azure AD provides you with the following benefits:
- You can control in Azure AD who has access to SAP Cloud Platform.
- You can enable your users to be automatically signed-in to SAP Cloud Platform (Single Sign-On) with their Azure AD accounts.
- You can manage your accounts in one central location – the Azure portal.
Prerequisite To configure Azure AD integration with SAP Cloud Platform, you need the following items,
- Azure Subscription
- Basic Azure knowledge
- An Azure AD tenant
- A SAP Cloud Platform Identity Authentication tenant
- A user account in SAP Cloud Platform Identity Authentication with Admin permissions.
- An Azure AD subscription. If you don’t have an Azure AD environment, you can get one-month trial here
- SAP Cloud Platform single sign-on enabled subscription
Definition Throughout the document, these terms are used,
- IaaS: Infrastructure as a service.
- PaaS: Platform as a service.
- SaaS: Software as a service.
Abstract This response document helps address standard Requests for Information (RFI) with which IoTCoast2Coast empower customers to evaluate different offerings in the market place today. Through the mappings available in the CCM, we can illustrate how Azure has implemented security and privacy controls aligned to other international standards such as ISO/IEC 27001, US Government frameworks including FedRAMP, and industry certifications such as PCI DSS. Complexity A cloud-specific controls framework such as the Cloud Control Matrix (CCM) reduces the risk of an organization failing to consider important factors when selecting a cloud provider. The risk is further mitigated by relying on the cumulative knowledge of industry experts who created the framework, and taking advantage of the efforts of many offerings. Comparison For organizations that do not have detailed knowledge about the different ways that cloud providers can develop or configure their offerings, reviewing a fully developed framework can provide insight into how to compare similar offerings and distinguish between providers. A framework can also help determine whether a specific service offering meets or exceeds compliance requirements and/or relevant standards.
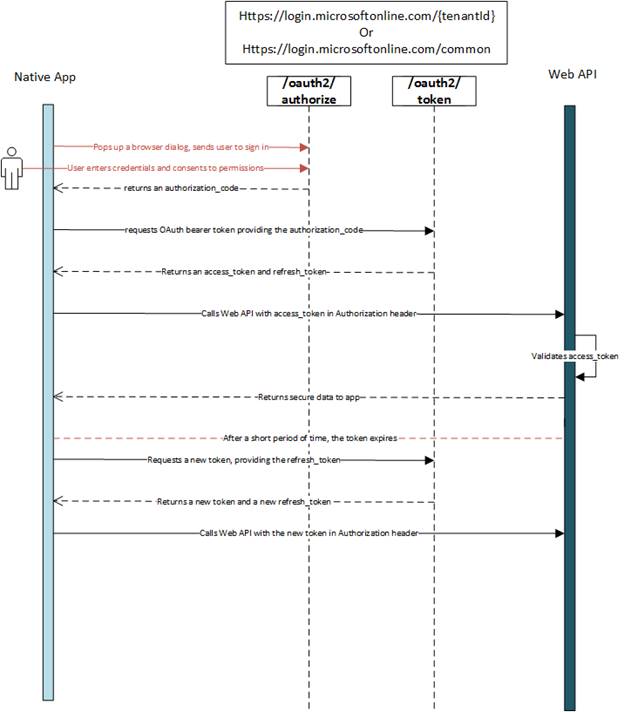
Authorize access to Azure AD web applications using the OAuth 2.0 code grant flow
Azure Active Directory (Azure AD) uses OAuth 2.0 to enable you to authorize access to web applications and web APIs in your Azure AD tenant. Register your application with your AD tenant First, register your application with your Azure Active Directory (Azure AD) tenant. This will give you an Application ID for your application, as well as enable it to receive tokens.
- Sign in to the Azure portal.
- Choose your Azure AD tenant by selecting your account in the top right corner of the page, followed by selecting the Switch Directory navigation and then selecting the appropriate tenant.
- Skip this step if you only have one Azure AD tenant under your account, or if you’ve already selected the appropriate Azure AD tenant.
- In the Azure portal, search for and select Azure Active Directory.
- In the Azure Active Directory left menu, select App Registrations, and then select New registration.
- Follow the prompts and create a new application. It doesn’t matter if it is a web application or a public client (mobile & desktop) application for this tutorial, but if you’d like specific examples for web applications or public client applications, check out our quickstarts.
- Name is the application name and describes your application to end users.
- Under Supported account types, select Accounts in any organizational directory and personal Microsoft accounts.
- Provide the Redirect URI. For web applications, this is the base URL of your app where users can sign in. For example, http://localhost:12345. For public client (mobile & desktop), Azure AD uses it to return token responses. Enter a value specific to your application. For example, http://MyFirstAADApp.
- Once you’ve completed registration, Azure AD will assign your application a unique client identifier (the Application ID). You need this value in the next sections, so copy it from the application page.
- To find your application in the Azure portal, select App registrations, and then select View all applications.
OAuth 2.0 authorization flow
At a high level, the entire authorization flow for an application looks a bit like this,
Azure Advanced Threat Protection (ATP)
Azure Advanced Threat Protection (ATP) is a cloud-based security solution that leverages your on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization. Azure ATP enables SecOp (Security Operation) analysts and security professionals to detect advanced attacks in hybrid environments in the following ways,
- Monitors users, entity behavior, and activities with learning-based analytics.
- Protects user identities and credentials stored in Active Directory.
- Identifies and investigates suspicious user activities and advanced attacks throughout all phases of a cyberattack.
- Provides clear incident information on a simple timeline for fast triage
Enterprise cloud directory Azure Active Directory is a comprehensive identity and access management solution in the cloud. It combines core directory services, advanced identity governance, security, and application access management. Azure AD makes it easy for your developers to build policy-based identity management into your organization’s applications. Azure AD Premium editions include additional features to meet the advanced identity and access needs of enterprise organizations, such as,
- The ability for someone to sign in to thousands of applications, including on-premises business applications as well as cloud-based and consumer apps.
- Multifactor authentication.
- Conditional access based on group and location, or device state.
- Azure IoT device-level authentication.
- Access monitoring and logging.
- Cloud App Discovery.
- Self-Service Password Reset (SSPR).
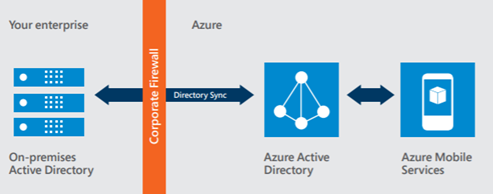
Azure AD enables a single identity management capability across on-premises, cloud, and mobile solutions.
The Azure AD Premium P2 edition offers three important features,
- Azure AD Identity Protection leverages the anomaly detection of Azure AD to detect anomalies in real time. It uses adaptive machine-learning algorithms and heuristics to detect indications that an identity has been compromised. With Azure AD Identity Protection, you can detect potential vulnerabilities affecting your organization’s identities, configure automated responses to detected suspicious actions that are related to your organization’s identities, investigate suspicious incidents, and take appropriate action to resolve them.
- Azure AD Privileged Identity Management helps you manage, control, and monitor access within your organization, by identifying Azure AD administrators, enabling just-in-time administrative access to online services, and providing reports and alerts about administrative access.
- Access reviews provide governance of identities to ensure users and administrators have the correct access to apps and resources over time. Access reviews enable IT organizations to review access to groups or resources and confirm they still need access to perform their tasks.
Multifactor authentication
The use of multiple authentication factors reduces the risk of unauthorized user access, such as through phishing attacks, and Azure MFA works for both on-premises and cloud applications and across both in a hybrid configuration, helping to safeguard access to data and applications. It delivers strong authentication through a range of easy verification options—phone call, text message, or mobile app notification—allowing users to choose the method they prefer for both on-premises and cloud applications. Conditional access Users can access your organization’s resources by using a variety of devices and apps from anywhere, so just focusing on who can access a resource is not sufficient anymore. You need to make sure that these devices meet your standards for security and compliance. With Azure AD conditional access, you can make automated access-control decisions for accessing your cloud apps that are based on conditions such as device state, location, client application, and sign-in risk. Azure IoT device-level authentication Authentication applies to devices as well as users, especially in today’s Internet of Things (IoT). Azure IoT supports X.509 certificates for enhanced authentication at the device level. Device identity can be transmitted safely and securely from the edge to the cloud. You can use the IoT Hub device identity registry to configure per-device security credentials and access control using tokens. Azure IoT Hub grants access to endpoints by verifying a token against the shared access policies and identity registry security credentials. Security credentials, such as symmetric keys, are never sent over the wire.
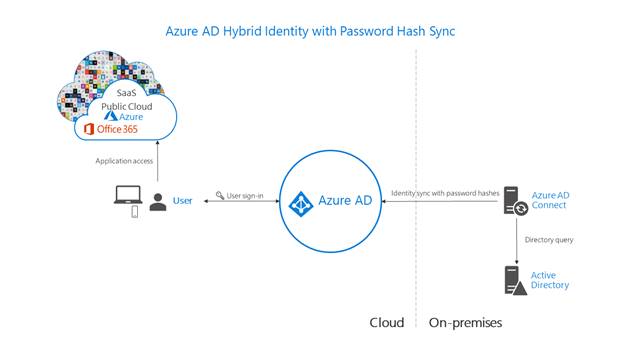
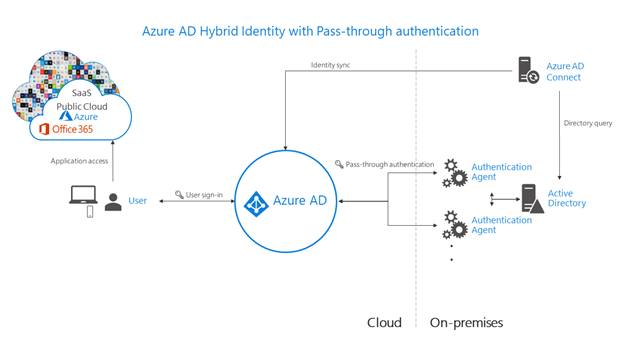
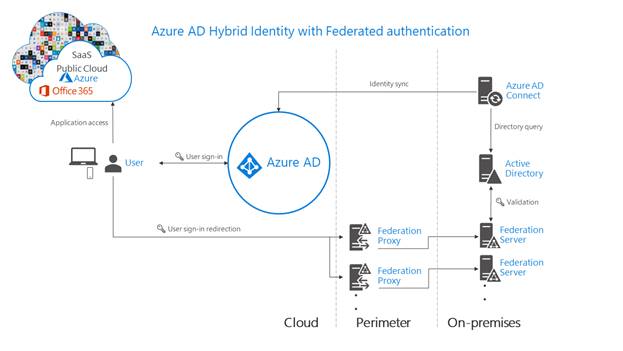
Architecture diagrams for AAD
The following diagrams outline the high-level architecture components required for each authentication method you can use with your Azure AD hybrid identity solution. They provide an overview to help you compare the differences between the solutions.
- Simplicity of a password hash synchronization solution,
- Agent requirements of pass-through authentication, using two agents for redundancy,
- Components required for federation in your perimeter and internal network of your organization,
Conclusion
This article outlines various authentication options that organizations can configure and deploy to support access to cloud apps. To meet various business, security, and technical requirements, organizations can choose between password hash synchronization, Pass-through Authentication, and federation. Consider each authentication method, like does the effort to deploy the solution, and the user’s experience of the sign-in process, address your business requirements? Evaluate whether your organization needs the advanced scenarios and business continuity features of each authentication method. Finally, IoTCoast2Coast evaluate the considerations of each authentication method as per business requirement and committed to implement best solutions as discussed above.
