Introduction
Let’s strengthen your security with Azure As you might know that cloud security covers every assets like Azure Resources, Networking, Data Protection (structured & unstructured), Active directory and much more. Let’s see how new Azure innovations, couple of them announced on Nov 4th , 2019 at the Microsoft Ignite Conference able to help us across security, compliance, and identity needs.

Prerequisite
- Azure Subscription
- Basic Azure knowledge
- Administrator Access
- PowerShell (Good to have)
Moving to the cloud
As organizations considering and evaluating public cloud services like Azure, AWS etc., it is essential to explore how cloud service models will affect cost, security, compliance, ease of use and privacy. It is equally important that customers understand that how security and compliance are managed by the cloud solution provider, in this case Microsoft enable a safe computing solution.
Many organizations that consider public cloud computing like Azure mistakenly assume that after moving to the cloud their role in securing their data shifts most security and compliance responsibilities to the Microsoft- THIS IS NOT TRUE.
Please don’t assume your resources are automatically protected, while Azure does ensure a secure infrastructure, you are responsible for ensuring protection of your data – not Microsoft.
Azure by design should provide security for certain elements, such as the physical infrastructure and network elements, but customers must be aware of their own responsibilities. MICROSOFT may provide services to help protect data, but customers must also understand their role in protecting the security and privacy of their data. The best illustration of this issue involves the poor implementation of a password policy; a CSP’s best security measures will be defeated if users fail to use complex or difficult-to-guess passwords.
It’s all detailed in Microsoft’s Shared Responsibility Security Model. Understanding where the Shared Responsibility model starts and stops is critical to ensuring your data is secure and compliant.
Welcome to Share Responsibility Security Model
Great News – Azure infrastructure adhered with many regulatory compliances like Azure CIS 1.1.0, PCI DSS 3.2.1, ISO 27001, SOC TSP providing 24×7 continuity from inside geographically dispersed datacenters.
In compliance with these standards, Microsoft provides security for physical assets, databases, monitoring and operations network infrastructure and availability. Within Azure, Microsoft assumes responsibility for general datacenter components such as compute hosts, datacenter assets, and the networks that connect them. Customers continue to be solely responsible for their user accounts, system endpoints, permissions/access controls and most importantly their data.
Customer data availability and integrity comes with the package when leveraging cloud, however retention, compliance, and rights management are the responsibility of the customer. Microsoft provides many features and tools (discussed below) to help with these challenges, but it is up to the customer to architect and implement the necessary policies and controls for their data.

A layered approach to security
Azure Security Defense is a strategy that employs a series of mechanisms to slow the advance of an attack aimed at acquiring unauthorized access to information. Each layer provides protection so that if one layer is breached, a subsequent layer is already in place to prevent further exposure.
Microsoft applies a layered approach to security, both in physical data centers and across Azure services. The objective of defense in depth is to protect and prevent information from being stolen by individuals who are not authorized to access it, Let’s take a look at each of the layers.
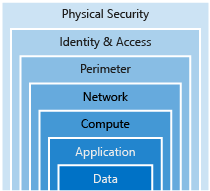
Data

Hackers LOVE data, it’s so precious for everyone. Below are Data storage options:
- Stored in a database
- Stored on disk inside virtual machines
- Stored on a SaaS application such as Office 365
- Stored in cloud storage
Secure the data can be ensured by controlling access to data only to group of people who need it. Later part of this document we will see step to secure the Data.
Application

Integrating security into the application development life cycle will help reduce the number of vulnerabilities introduced in code.
- Ensure applications are secure and free of vulnerabilities.
- Need to store sensitive application secrets in a secure storage medium like Key Vault .
- Make security a design requirement for all application development.
Compute

- Secure access to virtual machines.
- Implement endpoint protection and keep systems patched and current.
Malware, unpatched systems, and improperly secured systems open your environment to attacks. The focus in this layer is on making sure your compute resources are secure, and use the proper controls in place to minimize security issues.
Networking

- Limit communication between resources.
- Deny by default.
- Restrict inbound internet access and limit outbound, where appropriate.
- Implement secure connectivity to on-premises networks.
At this layer, the focus is on limiting the network connectivity across all your resources to allow only what is required. By limiting this communication, you reduce the risk of lateral movement throughout your network.
Perimeter
- Use distributed denial of service (DDoS) protection to filter large-scale attacks before they can cause a denial of service for end users.
- Use perimeter firewalls to identify and alert on malicious attacks against your network.
At the network perimeter, it’s about protecting from network-based attacks against your resources. Identifying these attacks, eliminating their impact, and alerting you when they happen are important ways to keep your network secure.
Identity and access

- Control access to infrastructure and change control.
- Use single sign-on and multi-factor authentication.
- Audit events and changes.
The identity and access layer is all about ensuring identities are secure, access granted is only what is needed, and changes are logged.
Physical security
- Physical building security and controlling access to computing hardware within the data center is the first line of defense.
With physical security, the intent is to provide physical safeguards against access to assets. This ensures that other layers can’t be bypassed, and loss or theft is handled appropriately.
1. Azure Sentinel
Microsoft launch new product & services on Nov 4th, 2019 like “Azure Sentinel”. Azure Sentinel is available to help security analysts, collect data from a variety of sources, including Zscaler, Barracuda, and Citrix. In addition, Microsoft also releasing new hunting queries and machine learning-based detections to assist analysts in prioritizing the most important events.
2. Azure Security Center
Azure Security Center is a unified infrastructure security management system that strengthens the security posture of your data centers and provides advanced threat protection & remediation suggestions across your workloads in the cloud.


Here we can see total 8 recommendations from 5 unhealthy resources.
Let’s see ‘Compute & apps resources’ recommendation

Compute recommendation ‘Diagnostic logs in Azure Stream Analytics should be enabled’, Secure Score, Failed Resources and Severity details will be found.
More Details about threats like Data exfiltration and threat resistance and Information can be find by clicking the Description.

Now it’s the time to re-mediate it, so scroll down and let’s fix the remediation.

Fix the issue:
For Manual remediation, follow the steps as mentioned above, alternatively scroll down and select the ‘Unhealthy Resource’ and click Remediate
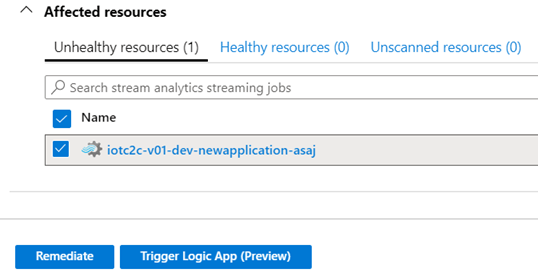
By Clicking Remediate 1 resource, you have mitigated Security vulnerability.
This is most secure and visualize platform. Azure ensure best Cloud security and rich tool-sets.
Need Cloud Security Solution for your Enterprise, please Contact me-Happy to help!!
Image Credit: Google

Good Information About Microsoft Azure Cloud. Sir, I have also written article about Microsoft Azure Cloud Free Trial https://www.prowebtips.com/free-microsoft-azure-get-200-credit/
If anyone want to know how to get trial subscription absolutely free of cost.
LikeLiked by 1 person