Introduction
Azure Governance provides mechanisms and processes to maintain control over your applications and resources in Azure. Azure customers get the most advanced set of governance capabilities. It involves planning your initiatives and setting strategic priorities. There should be a balance between “Agility” to the team and “Governance” to ensure team can work with best practices without compromising security and overhead cost.
Governance in Azure is primarily implemented with two services.
Azure Policy allows you to create, assign, and manage policy definitions to enforce rules for your resources. Stay compliant with internal and external regulations by configuring your templates using policies, access controls, resources, and then deploying them. This feature keeps those resources in compliance with your corporate standards.
Azure Cost Management allows you to track cloud usage and expenditures for your Azure resources and other cloud providers. Customers can ensure compliance at no additional cost, save significant amount of $ expenditures by proper resource management. Example drop unused resources, enable services like ‘Azure SQL Datawarehouse (ASDWH)’ ONLY when required. A lot of extra cost could be saved by automation of resources and correct storage decision.
Prerequisite
- Azure Subscription
- Basic Azure knowledge
- Administrator Access
- PowerShell (Good to have)
Five Disciplines of Cloud Governance
Let’s start cloud journey and a journey without a target destination is just wandering. It’s important to establish a rough vision of the end state before taking the first step. It’s not company starting point, but it shows potential destination.
Corporate policies: Corporate policies drive cloud governance. The governance guide focuses on specific aspects of corporate policy:
- Business risks: Identifying and understanding corporate risks.
- Policy and compliance: Converting risks into policy statements that support any compliance requirements.
- Processes: Ensuring adherence to the stated policies.
Five Disciplines of Cloud Governance: These disciplines support the corporate policies. Each discipline protects the company from potential pitfalls:
- Cost Management
- Security Baseline
- Resource Consistency
- Identity Baseline
- Deployment Acceleration
Essentially, corporate policies serve as the early warning system to detect potential problems. The disciplines help the company manage risks.
The following infographic provides a frame of reference for the end state.

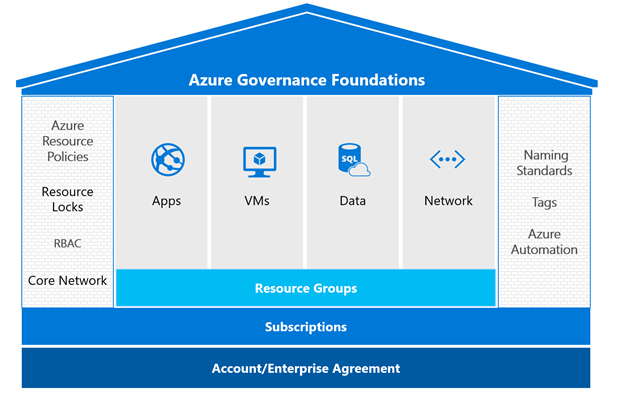
Governance basics
Following are the key components of the Governance for an Enterprise:
- Scope & Hierarchy
- RBAC
- Policy
- Azure Resource Manager Templates
Scope & Hierarchy
Resource group stay in a subscription; a subscription is container for the logically similar resources. Management group is additional level of hierarchy which help to administer subscriptions.

As per business need Management group hierarchy up to Six level (deep) can be created.

Role-based access control
Access management for resources is a critical function for any organization. Role-based access control (RBAC) helps you to manage who has access to Azure resources, what they can do with those resources, and what areas they have access to.
Following actions with RBAC:
• Allow one user to manage VM in a subscription and another user to manage virtual networks
• Allow a DBA group to manage SQL databases in a subscription
• Allow a user to manage all resources in a resource group, such as VM’s, websites, and subnets
• Allow an application to access all resources in a resource group
RBAC Recommended Practice
Using RBAC, you can isolate duties within your team and grant only the amount of access to users that they need to perform their jobs.
Instead of giving everybody open permissions in your Azure subscription or resources, you can allow only certain actions at a particular scope.
When planning your access control strategy, it’s a best practice to grant users the least privilege to get their work done. The following diagram shows a suggested pattern for using RBAC.

Security Principal
A security principal is an object that represents a user, group, service principal, or managed identity that is requesting access to Azure resources.
Security principal for a role assignment
User – An individual who has a profile in Azure Active Directory. You can also assign roles to users in other tenants. For information about users in other organizations, see Azure Active Directory B2B.
Group – A set of users created in Azure Active Directory. When you assign a role to a group, all users within that group have that role.
Service principal – A security identity used by applications or services to access specific Azure resources. You can think of it as a user identity (username and password or certificate) for an application.
Managed identity – An identity in Azure Active Directory that is automatically managed by Azure. You typically use managed identities when developing cloud applications to manage the credentials for authenticating to Azure services.
Azure Built-in Roles
FOUR FUNDAMENTAL built-in roles, please note ‘The first Three’ apply to all resource types:
Owner – Has full access to all resources including the right to delegate access to others.
Contributor – Can create and manage all types of Azure resources but can’t grant access to others.
Reader – Can view existing Azure resources.
User Access Administrator – Lets you manage user access to Azure resources.
Let’s Add some Roles for Enterprise
- Go to the Portal and click on the All Services
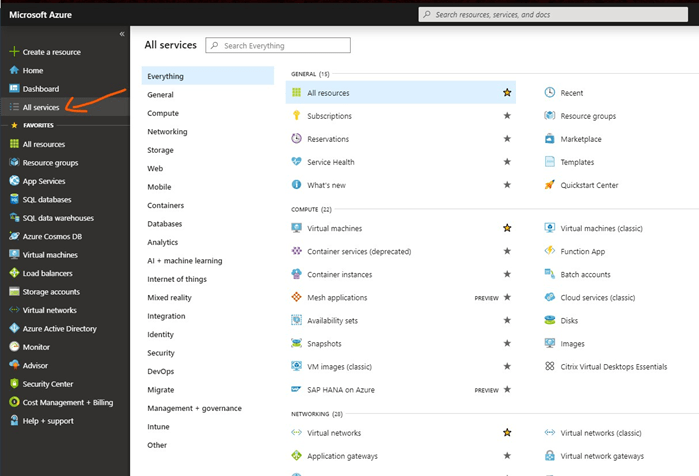
- Search Users and Select Users

- Add ‘New Guest User’, give our Email Address and Hit Invite

- Invited Guest will get Email notification (Sample Email) and they need to Accept it.

Azure Policy
Azure Policy allow us to have Real-time enforcement, compliance assessment and remediation at scale.
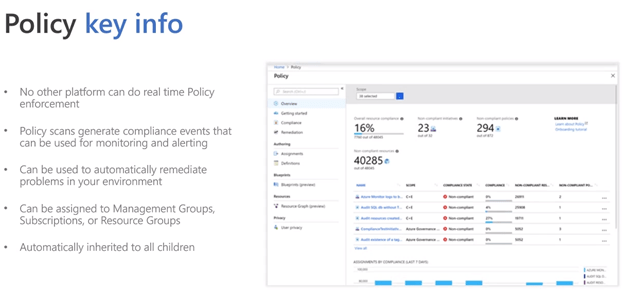
Let’s create new Policy
- Go to the Portal and type Policy in search window.

- Click on the Definition under Policy and give details:

Policy best practices

Azure Resource Manager (ARM)
Azure Resource Manager Template defines the resources you need to deploy for your solution.
Please note that Azure Resource Manager Template is a just a simple JSON file.

Governance Strategy

New Compliance Product: Welcome Azure Blueprints (PREVIEW)
Blueprints enable quick creation of governed subscriptions. This allows Cloud Architects to design environments that comply with organizational standards and best practices – enabling your app teams to get to production faster.
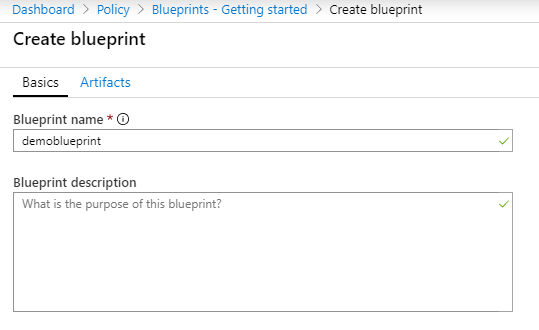
Let’s Create Azure Blueprint for Enterprise
The first step in defining a standard pattern for compliance is to compose a blueprint from the available resources. Here we will create a new blueprint to configure role and policy assignments for the subscription. Then we will add a new resource group, and create a Resource Manager template and role assignment on the new resource group.
- Select All services in the left pane. Search for and select Blueprints. We can create a blank Blueprint or sample Blueprint

- Select Blueprint definitions from the page on the left and select the + Create blueprint button at the top of the page.

Provide a Blueprint name such as DemoBlueprint. (Use up to 48 letters and numbers, but no spaces or special characters). Leave Blueprint description blank for now.
In the Definition location box, select the ellipsis on the right, select the management group or subscription where you want to save the blueprint, and choose Select.
- Add a role assignment at the subscription level
- Select the + Add artifact row under Subscription. The Add artifact window opens on the right side of the browser.
- Select Role assignment for Artifact type.
- Under Role, select Contributor. Leave the Add user, app or group box with the check box that indicates a dynamic parameter.
- Select Add to add this artifact to the blueprint.
Once you completed blueprint should look similar to the following.
Publish a blueprint
Now that all the planned artifacts have been added to the blueprint, it’s time to publish it. Publishing makes the blueprint available to be assigned to a subscription.
- Select Blueprint definitions from the page on the left.
- In the list of blueprints, right-click the one you previously created and select Publish blueprint.
- In the pane that opens, provide a Version (letters, numbers, and hyphens with a maximum length of 20 characters), such as v1. Optionally, enter text in Change notes, such as First publish.
- Select Publish at the bottom of the page.
Select Publish at the bottom of the page.
Azure Cost Management
Cost Management help enterprise with
- Analyze cloud costs
- Monitor with budgets
- Optimize with recommendations

Enterprise can easily understand Azure costs with
- Cost Analysis
- Cost alerts
- Budgets
- Advisor Recommendation
- Cloudyn
Conclusion
Bearing these factors in mind, it is important to consider how this applies to your organization. Any governance model will need to reflect the company’s strategic, compliance, and budgetary goals and requirements. One of first steps should be to model the organization’s hierarchy to map out the pattern for departments, accounts and subscriptions you will use in the Enterprise Portal.
Once you have taken billing and administrative factors into account to devise a subscription strategy, then the next step is to develop a centralized approach. The centralized approach makes it easier to build and maintain hybrid network connectivity, protect data sovereignty, and enforce compliance requirements within the environment.
References
https://docs.microsoft.com/en-us/azure/governance/azure-management
https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/govern/index
https://docs.microsoft.com/en-us/azure/cloud-adoption-framework/govern/guides/standard/

